Apple; baseline; configuration management; endpoint device security; macOS; macOS Security Compliance Project (mSCP); operating system security; security compliance.
https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-219-draft.pdf
This publication is available free of charge from:
https://doi.org/10.6028/NIST.SP.800-219-draft
Jamf Pro Extension Attributes for the mSCP (macOS Security Compliance project)
https://github.com/hardstriker/mSCP_EAs/blob/main/mSCP-FailedResultsList.xml
Checking out older versions
As per getting started: check to work locally, first clone into the repository and install the required Python3 modules and Ruby gems:
Getting Started: from macOS Terminal
a. git clone https://github.com/usnistgov/macos_security.git
b. cd macos_security
c. pip3 install -r requirements.txt --user
d. bundle install
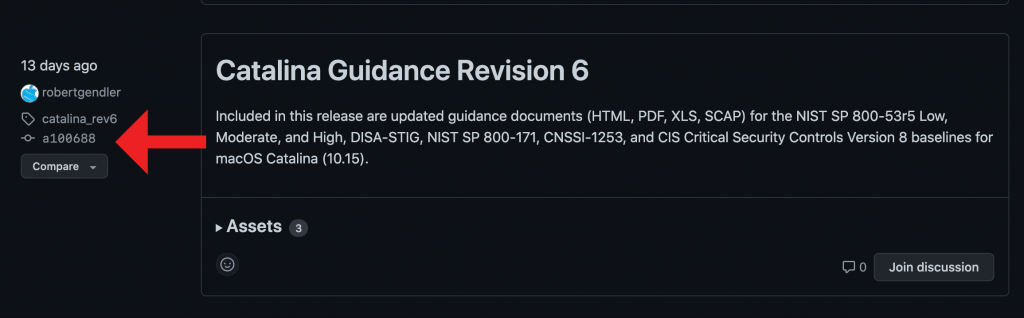
1. older macOS Security Releases from Github: This project is Catalina Guidance Revision 6
Photograph of Git checkout (a100688) I am using to load the older Catalina STIG
Follow these steps in Terminal
Link to updated-legacy Catalina resource(s).
1. Get Catalina to overwrite current (Monterey) resources locally
https://github.com/usnistgov/macos_security/releases/tag/catalina_rev6
git checkout a100688
switch
git switch -c a100688
Baseline(s)
Baseline files are used for the creation of the guide, scripts, and mobileconfig files. Each baseline defines the associated controls which are used to meet a given security profile.
2. Generate STIG baseline:
If you want to create your own baseline or modify an existing baseline, the generate-baseline.py found in the scripts folder will generate a {baseline}.yaml file containing all the rules corresponding with the provided tag (baseline). This {baseline}.yaml is required to run the generate-guidance.py script.
Run this for the STIG
sudo ./scripts/generate_baseline.py -k stig
generate-baseline.py Usage
python3 scripts/generate_baseline.py -h
usage: generate_baseline.py [-h] [-c] [-k KEYWORD] [-l]
Given a keyword tag, generate a generic baseline.yaml file containing rules
with the tag.
optional arguments:
-h, --help show this help message and exit
-c, --controls Output the 800-53 controls covered by the rules.
-k KEYWORD, --keyword KEYWORD
Keyword tag to collect rules containing the tag.
-l, --list_tags List the available keyword tags to search for.
Link: https://github.com/usnistgov/macos_security/wiki/Baselines
—- EOF Baselines
Guidance
3. Generate STIG Mobile Configuration Profiles (-p)
sudo ./scripts/generate_guidance.py -p build/baselines/stig.yaml
Generate code signed STIG Mobile Configuration Profiles (-p) (-H) with hashvalue
sudo ./scripts/generate_guidance.py -p -H
python3 ./scripts/generate_guidance.py -h
usage: generate_guidance.py [-h] [-l LOGO] [-p] [-r REFERENCE] [-s] [-x] [-H HASH] baseline
Given a baseline, create guidance documents and files.
positional arguments:
baseline Baseline YAML file used to create the guide.
optional arguments:
-h, –help show this help message and exit
-l LOGO, –logo LOGO Full path to logo file to be included in the guide.
-p, –profiles Generate configuration profiles for the rules.
-r REFERENCE, –reference REFERENCE
Use the reference ID instead of rule ID for identification.
-s, –script Generate the compliance script for the rules.
-x, –xls Generate the excel (xls) document for the rules.
-H HASH, –hash HASH sign the configuration profiles with subject key ID (hash value without spaces)
4. Generate STIG Guidance Script (-s)
sudo ./scripts/generate_guidance.py -s build/baselines/stig.yaml
The supplied macOS Security Compliance Project (mSCP) Portable Network Graphics is a raster-graphics file type logo is a large 1024×1024 pixels in size; also note to save this in the more compressed-legacy compatible format available to your graphics program. I also had to experiment with reducing the sizes of the custom logos. To apply a new logo note the (-l) followed by the path to your png file.

NOTE: VARIATION -> Generate STIG Guidance Script (-s), Excel file (-x) and Path to custom logo (-l)
a.
./scripts/generate_guidance.py -s -x -l /Users/username_here/Library/Application\ Support/macos_security/templates/images/YOURLogo_logo.png build/baselines/stig.yaml 5. Generate STIG Rules Export to Excel
sudo ./scripts/generate_guidance.py -x build/baselines/stig.yaml
Big Sur Guidance: (REPEAT STEPS 1-4 AFTER following this step)
https://github.com/usnistgov/macos_security/releases/tag/big_sur_rev5
git checkout 3903e57
– 3903e57
Monterey Guidance: (REPEAT STEPS 1-4 AFTER following this step)
https://github.com/usnistgov/macos_security/releases/tag/big_sur_rev5
git checkout e8cdc49
– e8cdc49
Undo Git Commit to older Catalina from 1st steps above:
git switch –
Link:
https://github.com/usnistgov/macos_security/wiki
https://golbiga.medium.com/getting-to-know-macos-security-compliance-project-part-1-31d0689b7c30
Cloning older gits
https://stackoverflow.com/questions/12256137/cloning-an-older-version-of-github-repo
Previous releases
https://github.com/usnistgov/macos_security/releases
Instructions for Generating DISA STIG Guidance – Catalina rev6
1. Downloaded https://github.com/usnistgov/macos_security/archive/refs/tags/catalina_rev6.zip
2. Saved to Desktop and unzipped:
cd ~/Desktop/macos_security-catalina_rev6/
3. Generate a baseline
sudo ./scripts/generate_baseline.py -k stig
4. Generate Profiles
sudo ./scripts/generate_guidance.py -p build/baselines/stig.yaml
5. Generate guidance
sudo ./scripts/generate_guidance.py -s build/baselines/stig.yaml
6. Generate Excel guidance: Generate the excel (xls) document for the rules.
sudo ./scripts/generate_guidance.py -x build/baselines/stig.yaml
——————————–
IMPORTANT NOTES REGARDING Editing the compliance script so it can be loaded into Jamf MDM
————–
remove everything after
echo “$(date -u) Remediation complete” >> “$audit_log”
}
—————————–
Generate Oval Content
The generate oval script creates the OVAL checks required for SCAP generation. Link
python3 scripts/generate_oval.py -h
usage: generate_oval.py [-h] baseline
Given a profile, create oval checks.
positional arguments:
baseline Baseline YAML file used to create the oval.
optional arguments:
-h, –help show this help message and exit
cd /Users/USERFOLDER/Library/Application Support/macos_security/scripts
Utilizing this
python3 scripts/generate_oval.py baselines/DISA-STIG.yaml
–
./generate_jamf.py -j /Users/edarnold/Library/Application\ Support/macos_security/baselines/DISA-STIG.yamlpython3 ./generate_jamf.py -j /Users/edarnold/Library/Application\ Support/macos_security/baselines/DISA-STIG.yaml
————– EOF Oval instructions
—————– new code below
echo "$(date -u) Remediation complete" >> "$audit_log"
}
and add
case $4 in
--check)
check=0
run_scan
;;
--fix)
fix=0
run_fix
;;
*)
exit 0
;;
esac—————– check fix
then under the policy where you add the script you can add –check or –fix
————–
