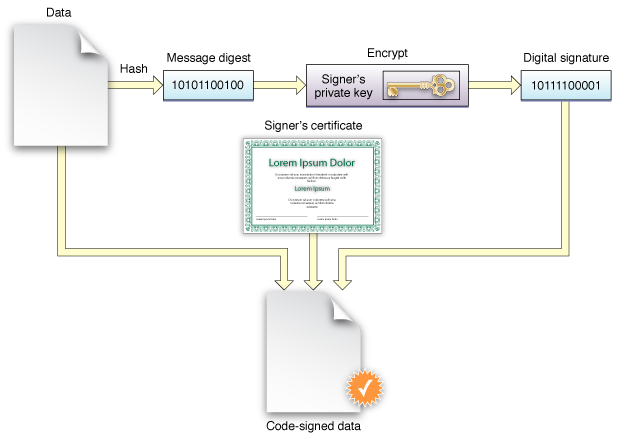
Security: Signed packages, profiles, and configurations help ensure the authenticity and integrity of the contents. When an item is signed using a digital certificate, it creates a unique digital signature. This signature makes it possible to verify that the item has not been tampered with and that it originates from a trusted source.
Identity Verification: Signing packages, profiles, and configurations allows Jamf Pro to verify the identity of the developer or organization that created them. This is particularly important in enterprise environments where IT administrators want to ensure that the software and configurations being deployed to devices are from trusted sources.
Compliance: In many organizations and industries, there are strict security standards and compliance requirements. Ensuring that all software and configuration deployments are signed helps maintain compliance with these standards, as it demonstrates that the organization is taking necessary precautions to protect its data and devices.
Compatibility: Some Apple features, such as Gatekeeper and Mobile Device Management (MDM), require signed packages and profiles. Signing your packages, profiles, and configurations ensures that they will be compatible with these features and can be successfully deployed to your devices.
Streamlined Deployment: Signing packages and profiles can help streamline the deployment process. When packages and profiles are signed, they can be trusted by the devices they are being installed on, reducing the likelihood of installation errors or user prompts that may interrupt the deployment process.
Overall, signing packages, profiles, and configurations in Jamf Pro is an important security practice that helps protect devices, data, and users in an enterprise environment. It helps ensure that only trusted software and configurations are deployed to devices, while also meeting compliance requirements and providing a smoother deployment experience.
Code signing is a macOS security technology that you use to certify that an app was created by you. Once an app is signed, the system can detect any change to the app—whether the change is introduced accidentally or by malicious code.
You participate in code signing as a developer when you obtain a signing identity and apply your signature to apps that you ship. A certificate authority (often Apple) vouches for your signing identity. Link: